You have an important contract you need to send to a client. How do you assure the client receives the document without it being tampered with? How does the client verify the document actually came from you?
This basic workflow has been in place for contracts between individuals, corporate entities, the food supply chain, and the hardware supply chain since the beginning of commerce. To generalize these workflows, I’ll use “artifact” to represent a “document”, “software package,” or “hardware thingy”.
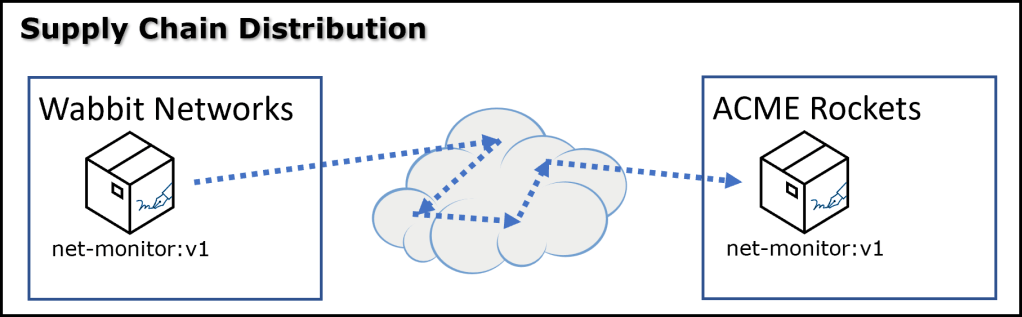
Every supply chain needs to securely distribute artifacts from a source to one or more destinations. The receiver must be assured the artifact arrived intact (not tampered with), and that it came from an identity they trust. How it got from A to Z is interesting, however assuring it arrived intact is core to assuring the supply chain’s integrity.

Regardless of industry or artifact type, the basics are the same. The producer seals the artifact with a tamper-proof seal, stamping it with its identity. The consumer verifies the integrity, and who sealed it. Additional context may be added to the tamper-proof seal, such as statements of quality to industry standards.
With the identity and integrity in place, the real evaluation can then begin as the quality and the information about the artifact can only have value, if you trust the source.
Why Not Just Pick It Up?
The alternative to trusting an end-to-end supply chain is to simply “pick up the artifact” from the trusted location. In the physical world, you may travel to a physical location that is hard to spoof. This is an obvious challenge as it involves time and resources to travel, retrieving each artifact. In the digital world, where everyone is continually connected to the internet, you could easily pick up the artifact directly from the producer. Does the issuer of the HTTPS certificate give any more or less confidence than a physical location? If you directly picked the artifact up, does an integrity seal matter? And, do you need to associate an identity with the tamper-proof seal?
The reality is that delivery and pickup are rarely between two individuals. Rather many individuals play a role in the creation, distribution, transportation, receivership, internal verification, and internal distribution. The artifact travels through many “hands” that have an opportunity to alter the artifact.
Even in the most simplistic scenarios, being able to maintain a trusted chain of custody would be near impossible, or certainly impractical to manage. This is why industries have moved to seal the integrity with an identity. As the artifact moves across the supply chain, efficiencies come into play, where multiple artifacts are bundled in a container. In this case, I’m talking about a physical shipping container, a distribution truck, or other means to efficiently package independent items, with independently sealed identities as they travel across a supply chain.
The same can be said about pulling digital content across “the network”. How does one seal various packages within a docker container as its distributed across a supply chain? The network may be public, private within a company, or air-gapped through a data-diode., Assuming a dependency on an external entity is a setup for disaster waiting to happen. Any one of the various points across the network may be unavailable, or any point across the network may be compromised.
Supply chains reliably function by having a buffer of artifacts close by, ready for use. The ingress of that buffer goes through a stage of quality control, to assure the artifact is what it was intended to be, from the anticipated sources, and the quality is appropriate for the target environment.
These are just some of the reasons we sign and seal artifacts for distribution, whether locally or globally distributed. Sealing an artifact doesn’t assure its quality, but it does assure it was sourced from a trusted identity and distributed intact for further evaluation.
Sealing the Integrity
You have an artifact that must travel to your client. How do you seal the integrity to assure it’s unaltered by the time it’s received? And, when is it important to do so?
Case Study: The Johnson & Johnson Tylenol Crisis
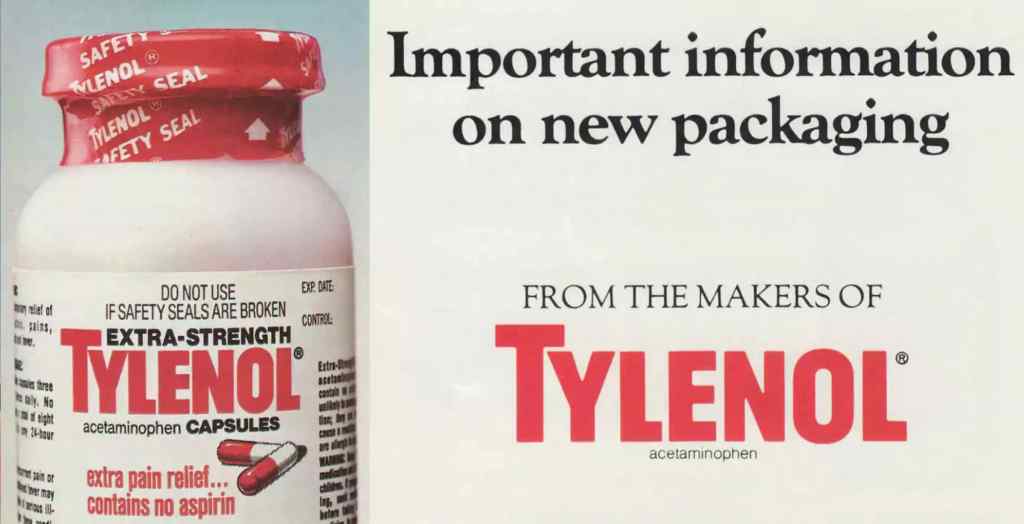
During the fall of 1982, a malevolent person or persons replaced Tylenol Extra-Strength capsules with cyanide-laced capsules, depositing them on the shelves of pharmacies and food stores in the Chicago area. The standard at the time allowed unsealed bottles to be distributed and placed on shelves. Seven unsuspecting people died a horrible death. Johnson & Johnson, which makes Tylenol, suddenly, and with no warning, had to explain to the world why its trusted product was suddenly killing people.
Spoiler alert, Johnson & Johnson moved to placing triple integrity seals, with lot identifiers for remediation.
Today, (2023), as you open your favorite beverage, you anticipate that “pop” sound of the vacuum seal breaking, or the “crack” of the plastic seal breaking. If you don’t hear or feel it, you likely have an instant emotional response. And, if you have teenagers, likely wonder if they’ve filled your alcohol bottle with water. The point is the industry shifted to what’s obvious now, but wasn’t so obvious at the time.
40 years later, are all products sealed? The summer of 2019 led to a viral trend: Licking ice cream, putting it back on the shelf As a result, Blue Bell Ice cream is now considering: “…looking at methods to add additional protection to the carton.”
That was 4 years ago. The other day, I brought home two different containers of ice cream. One had a plastic seal, the other didn’t, and I had to instantly look for any “impressions” – yuck.
Identity of the Seal – Signatures
Is it good enough to simply “seal” the artifact? Prior to 1982, medications were distributed with labels and a cap. The label provided the identity, but the cap was simply placed on the bottle. Now that integrity seals are “standard”, what would stop a bad actor from re-sealing the artifact as tamper resistant seals are easily available for purchase?
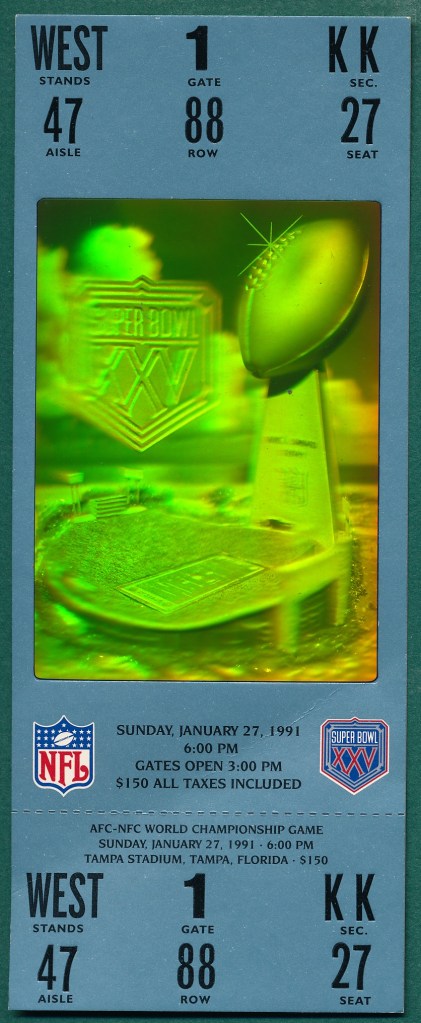
Placing a brand, on the integrity seal associates an identity with the sealing operation. Consider event tickets are some of the biggest scamming targets. And, what are some of the most expensive tickets? The 1991 Super Bowl featured holograms on the tickets. This represented some of the best technology of the time as it was quite difficult to fake a printed hologram.
2023 standards have evolved to digital tickets, where an app presents a verifiable barcode. Rather than exchanging physical tickets, digital tickets can be sold and transferred to others.
Not All Signatures Are Created Equally
There’s an identity associated with the ticket, the artifact in this case. As the consumer, co you trust the brand associated with the artifact? For event tickets, it’s rare to purchase directly from the artist or even the event coordinator. You may purchase from well-known trusted brands like ticketmaster, stubhub or seatgeek. However, “buyer beware” when finding individuals on craigslist offering great deals that just need you to Venmo some money, for the promise of tickets being sent. The craigslist brand identity may be accurate, but should you trust the individuals? There are many, even most, well-intended individuals on craigslist. If not, the site wouldn’t continue to exist. However, the craigslist brand is intentionally broad, enabling a wider marketplace. In this case, the “identity” of the distributor does not translate to endorse all the artifacts within that distributor, and that’s ok.
Associating Identity With an Artifact
In software, an identity is represented through a signature. A privately held signing instrument is used to produce a signature representing an individual or an entity. The signature is what’s made public, and a public certificate is used to compare the signature. But, how is the signature associated with the artifact, and what does the signature represent?
In software, there are two major categories of signatures. Embedded and Detached signatures. There are pros and cons to each, but there’s also the question of what can be inferred if the signature is embedded or detached.
Embedded Signatures
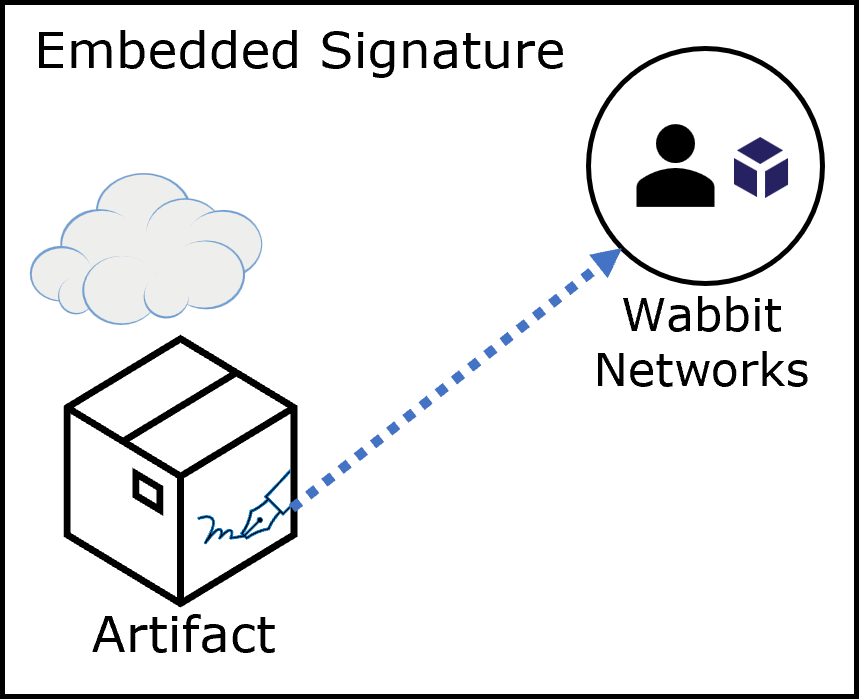
If the signature is embedded within the artifact, there’s a clear association. The issuer of the signature produced the artifact. That has real meaning. Consider what it takes to evaluate the signature to assure it’s from a trusted identity. Evaluating an attached signature is a classic trojan horse opportunity. To verify the signature, you must first take possession of the artifact to extract and evaluate the signature. You may determine the signature is invalid, or from a known bad actor. However, once you’ve downloaded the artifact, all it takes is another attack vector to access or activate it.
There are safe strategies for evaluating embedded signatures. You may download the artifact into a quarantined environment, such as the gated area in front of the fortress. The gated area can be flushed evicting the trojan horse, or if proven safe, the artifact may be allowed through the gates to the secured area. This is the classic quarantine pattern used when downloading content through your brower and best practices for Consuming Public Content
Detached Signatures
The alternative is detached signatures. But what does a detached signature represent? And, are detached signatures unique to software?

You’re travelling internationally, and you’re about to go through passport control. Your passport is a detached document that has your signature, representing your identity. You hand your passport through the opening to the passport officer who evaluates it. The passport has a signature, but it also has some additional context that says you have been vetted by the government that issued the passport. It’s more than just your identity, your passport is a statement that says the government that issued it has qualified you for international travel. It may have issued a Visa stamp (an additional statement) that associates permission to specific countries.
The passport has a detached signature that can be evaluated before you, the potential trojan horse, is permitted through. Your identity is verified, then compared to various security lists, such as the TSA no fly list. You are not permitted into the secured area, until you’ve been verified.
This detached signature pattern is just as applicable to software, and very powerful.
Multiple Detached Signatures
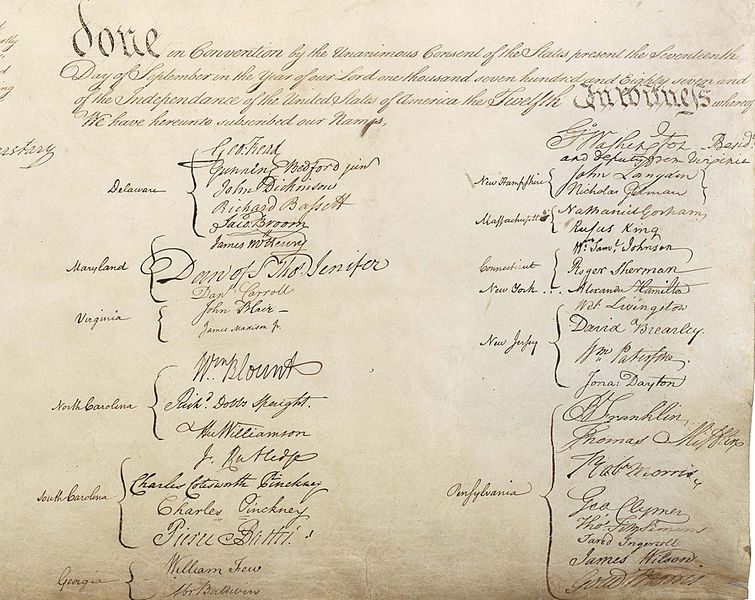
A collection of attached signatures would imply all the parties created the artifact, such as the United States Consitution.
What does it mean to have multiple detached signatures?
Just as the passport associates a signature with a statement the individual has been verifiably certified by the issuing government, detached signatures must also include some additional statement, otherwise the signature has no meaning. The signature might be a statement the artifact is considered harmful, or outdated in lieu of a newer version. Detached signatures require some additional context.
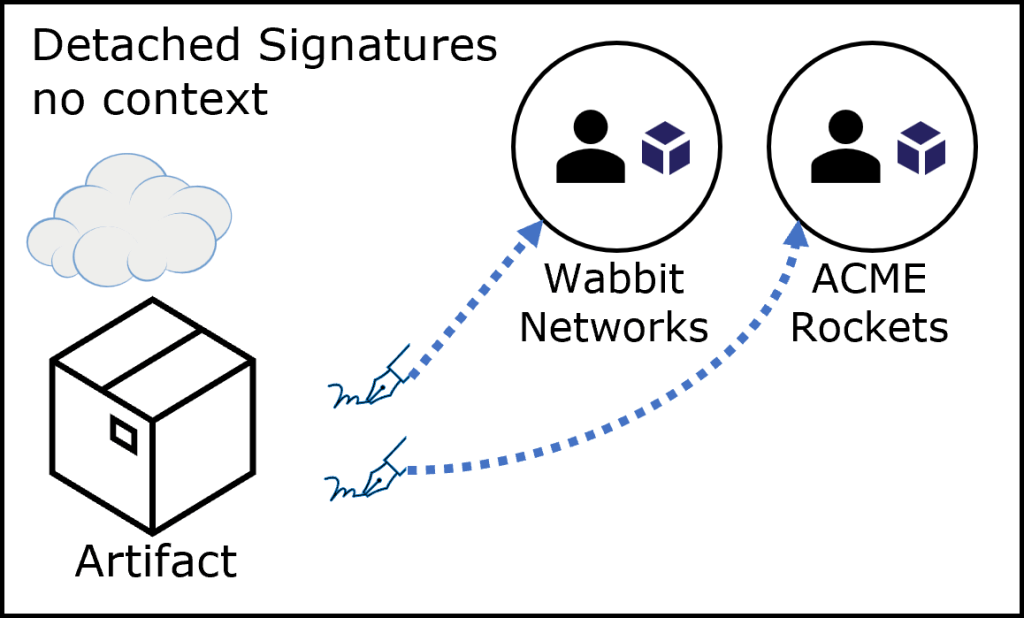
That additional context is a powerful tool, as it also allows different identities to make the same or different statements about an artifact.
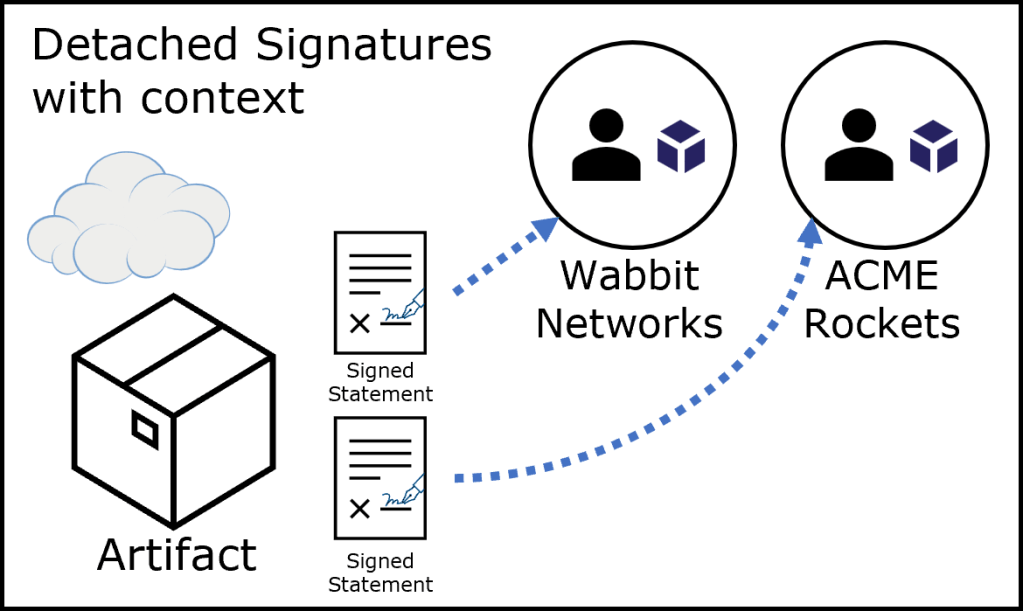
In the above example, Wabbit Networks made a statement they “created” the artifact on January 1st 2023, and certified it met a “network certification NA12-42a” standard as of that date. It was scanned using clair security scanning and found zero vulnerabilities on January 1st, 2023.
ACME Rockets scanned the artifact as they pulled it into their secure environment and approved it for use in medium- security environments.
The ability to associate an identity with a statement, as it reflects an artifact is a powerful capability. It’s also not limited to the point where the artifact was created. I’ll cover updates in a future article to deal with time-shifted discoveries.
Summing It Up
In this article we covered why associating a signature with an artifact is important to seal the integrity, with the opportunity to provide additional context. A signature is the result of a privately held signing instrument producing said signature, with a means to verify the signature is valid, and truly associated with the identity, Being able to verify and trust the identity is critical, as the content of the artifact is said to have zero trust if the identity can’t be verified. If the signature can’t be verified, does it add or distract value? And, just because an identity is verified, doesn’t mean you may choose to trust it. Or, you may choose to trust it for a particular environment?
We covered embedded and detached signatures as a means to provide additional statement about an artifact. Those statements may be positive or negative statements, and multiple entities may make the same statement. You then choose which entities you trust, just as you may apply information of your trusted advisors over random information you find on the internet.
In future articles, I’ll continue to tease out the elements for building a secure supply chain, mapped to familiar scenarios that have been tried and tested.

